If you have ever needed to track down the owner of a Microsoft Form, you likely have run into a dead end or a frustrating round of trial and error. Whether the Form was created for collecting data, creating a quiz for your Class Team, or some other reason I’m here to tell you there’s a better way to find some answers!
Continue readingIntro To Microsoft Teams Live Events – Resources
As promised during my Live Events talks in 2020, here are companion resources to go along with the tips we discussed.
Continue readingHelp! I Can’t Join a Microsoft Teams Channel Meeting!
As we have become more comfortable with the concept of working within a Team in Microsoft Teams, I see more and more people using Channel Meetings instead of the familiar meeting scheduled through an email client. With that transition, I have also saw an odd issue reported a few times recently that required a little investigation.
In the usual Channel meeting experience, members of the Team will see a post in the channel that the meeting was started in along with a “Join” button to participate in the action.
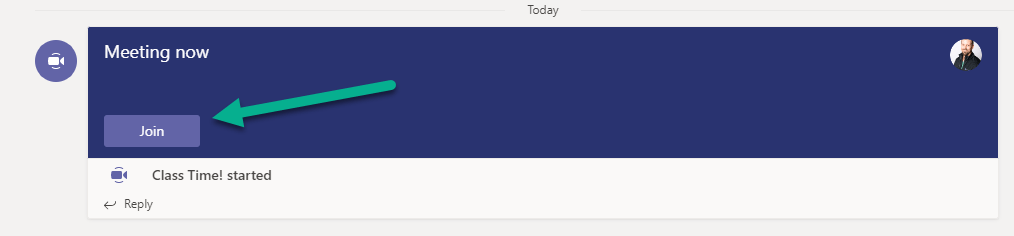
For the reported scenario, though, a Channel meeting is actively in progress however, someone (or multiple someones) report that they are unable to join. This issue goes beyond the usual challenges that we see with joining online meetings. In this case, we can see that the meeting has started but they do not even see a “Join” button in the channel to attempt to participate in the meeting.
Continue readingSit Courtside of the NBA Restart with Microsoft Teams
As of late, Microsoft is no stranger to getting involved in the world of sports. Back in 2017 the NFL and Microsoft agreed to a five year deal that would keep the Surface as the tablet of choice on sidelines around the league. Earlier this year, the two got a little closer and made history by using Microsoft Teams to conduct the first virtual NFL draft after the COVID-19 pandemic caused a worldwide shutdown.
Sports are now trying to make a comeback, though mostly without fans. The NBA decided the best move was to create a “bubble” wherein all involved with the league would be quarantined in Florida on Disney campus. Without fans in the stands, they needed to get creative with keeping them involved. After the success the NFL had with Microsoft, the NBA struck a deal to use the newly released “Together Mode” in Microsoft Teams meetings to bring fans…together.
Together Mode reimagines traditional virtual meetings, and according to research conducted by Microsoft is actually less fatiguing than a traditional meeting. Instead of a strict grid layout, all meeting participants look as if they are sitting theater style just like they would be in a sports arena making it fit perfectly with a virtual fan experience.
How are these “meetings” working?
Based on various pieces of information, it is becoming more clear how they are handling the fan experience. First, these are just Teams meetings with a virtual lobby. Each team has meeting moderators that are letting fans into the meeting as seats are available. The moderators are also responsible for removing any fans who become unruly. The terms and conditions state that you should be on camera for the entirety of the event and if you leave your seat or go off camera, risk being removed from the meeting so someone else can fill the seat. It also seems that you are getting a unique account in the NBA bubble tenant as the directions say that you will receive a username/password for Teams in your acceptance email. Going through some recent Teams meetings that were open to the public, I can sympathize with the NBA in coming up with the procedures for making this work as smoothly as possible.
Enough Of The Details…How Do I Get My Seat??
So how can you get courtside and experience this unprecedented virtual fandom using Microsoft Teams? It seems that each NBA team is taking their own approach to allowing fans access. Some just have open sign ups, others are partnering with Michelob Ultra to do a giveaway of virtual seats, while others are only offering tickets to existing season ticket holders or other VIPs.
Below are a list of opportunities I was able to find at the time of writing this blog if you’d like your shot at sitting courtside, virtually.
Boston Celtics – The Celtics have communicated that only season ticket holders, wait list members, corporate and community partners, etc are currently able to get tickets. Your best shot here is to become a season ticket holder asap.
Indiana Pacers – The Pacers have an open sign up so make the jump to get your chance!
Miami Heat – The Heat held an open sign up, but currently say they are sold out. You can still get on their waiting list though if you’d like a chance to cheer for them.
Memphis Grizzlies – The Grizzlies partnered with Michelob Ultra so you can sign up for the raffle for your chance to be a Grizz fan.
Phoenix Suns – The Suns have open sign ups with spots available.
Sacramento Kings – The Kings also partnered with Michelob Ultra so enter the raffle for a chance.
Washington Wizards – The Wizards want to make sure you REALLY want to cheer for them. To win a courtside seat you need to submit a video. Selected video winners will get their virtual fan opportunity.
The rest of the teams in the bubble either haven’t published how to get an opportunity (or I couldn’t find it) or have hid it really well. Good luck and have fun out there!
Quoted Replies in Microsoft Teams Private Chats
As Microsoft Teams continues to gain traction, and I find myself part of more 1:1 and 1:many chats in Teams I frequently see confusion about who is replying to which message in an active chat. This is much more common when the replies are flying at a frantic pace causing messages to lose context.
The Teams mobile app has a built in swipe function to quote a message and reply making it clear where the the reply is joined. Simply swipe right on a specific message and hit the reply button which will quote the message and start the reply dialogue:
When using the desktop app, though, quoting a reply is not as intuitive. It can still be done, and I use it often. Simply copy the text you’d like to quote, then start a new message with the ‘>’ character. This will initiate a quote box that you can paste the text into before replying.
As @TheVarnish made clear to me when I showed him, this isn’t exactly the same functionality that exists in the mobile app. I’ll give you the same advice I gave him 😊…there are plenty of uservoice requests for the functionality, and I would suggest you vote for the feature if it is something you’d like.
