I hear the question all of the time, “how do I get a list of attendees from my Teams meeting”? The reasons vary from a teacher wanting to make sure all students attended class, a business needing to track attendees of a training, etc. So how can we get that list?
Grab an admin
While the functionality exists, you need to start with getting it enabled which requires either a Global Administrator in your Microsoft 365 tenant, or someone with the Teams Administrator role.
As of the time of this writing, it must be enabled via the Skype for Business Online PowerShell module. I would expect this to become a GUI option at some point though. After connecting to the SFBO module, enable the ability to download a roster by running:
Set-CSTeamsMeetingPolicy -Identity Global -AllowEngagementReport "Enabled"Keep in mind that after running this command, it will take a little time before you start seeing the option in meetings…so take a nap, grab a beer, or just wait until tomorrow before you tell anyone to try it out.
It’s enabled so give me my roster!
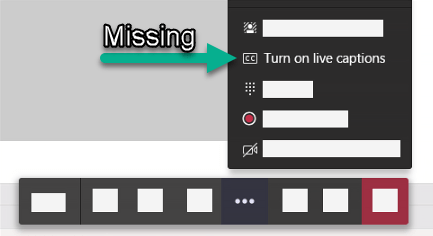
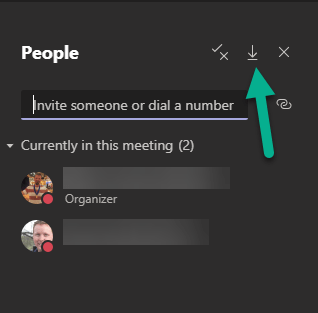
Only the meeting organizer is able to download the roster, so other presenters or attendees won’t even see the option. The meeting organizer, though, will see the option below which is going to download a CSV with info about attendees. You will be able to see when someone joins, leaves, etc. Additionally, there is a timestamp of the time the person joined.
Gotchas
This is a great addition that I’ve heard asked about many times, but there are some gotchas. I expect there to be improvements as time goes along so stay tuned!
GOTCHA #1: If someone joins the meeting prior to the organizer, the join timestamp currently shows the same time that the organizer joins. I don’t see that being a big issue in the majority of cases but just be aware.
GOTCHA #2: This is only giving you the roster of who joins or leaves while the organizer is in the meeting. If someone joins and leaves before you arrive you won’t capture them in the log.